this article outlines the key practices and implementable steps required for querying, log collection, storage and auditing of ip and domain names in the singapore cloud environment to help the operation and security teams balance compliance, availability and forensic capabilities.
on any cloud platform, reasonable logging scope usually includes: host/system logs, application logs, identity authentication and access logs, network traffic/flow logs, dns and address query logs, and cloud platform operation audits (such as api calls), etc. for these categories, retention times should be set based on compliance requirements and incident response needs. for example, the common retention period for general operation and maintenance and error troubleshooting is 30–90 days; it is recommended to retain audit logs required for compliance or evidence collection for 1–7 years. for services deployed in singapore, you should refer to local regulations (such as singapore's personal data protection act pdpa) and industry standards (financial, medical and other industries may require longer retention periods), and make a trade-off between sla and cost.
key logs related to address queries include dns query logs, reverse dns record access logs, http access logs of load balancing and waf, and network flow logs (such as vpc flow logs). in security audit scenarios, the most important thing is the type of logs that can restore access links: authentication and authorization logs (who accessed resources when and how), api call audits (change records), and network layer traffic logs can help identify abnormal outreach or lateral movement. the priority is usually: identity authentication log > network flow log > dns/address query log > application/business log.
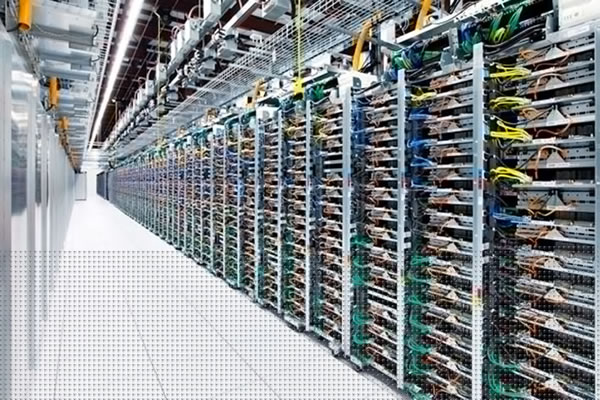
the implementation path can be divided into four steps: data collection, transmission, processing and storage. the collection end can use lightweight agents (such as filebeat, fluentd, syslog) or log service agents provided by cloud vendors to ensure that dns, system and application logs are pushed in real time. address query can use the built-in parser, dns query forwarding and parsing logs (such as turning on dns query logging), and record the external ip and domain name at the application layer. the transport layer recommends using tls/encrypted channels and combining message queues (kafka) or object storage for buffering. in the processing step, elk/efk or siem are used to structure, index and correlate the logs to facilitate auditing and traceability.
for log centralization, you can choose a hosted siem solution, a cloud vendor's log service, or a self-built elk cluster. for environments deployed in singapore, priority is given to storing logs in geographically close areas to reduce latency and meet data residency requirements. key principles include: using read-only archives (cold storage) to preserve historical audit logs, enabling encryption of transmitted and stored data, tiering storage to control costs, and restricting access through iam and key management (kms). to ensure auditability, it is recommended to save a complete copy of the original log and retain an audit chain for write operations. using worm or an immutable storage mechanism can enhance forensic credibility.

conducting security audits is not only a compliance requirement, but also a core practice for reducing security risks and improving incident response capabilities. specific to the singapore market, companies often face data protection regulations, cross-border data transfer reviews, and high compliance thresholds in the financial and medical industries. meticulously recording the address query and access logs of singapore cloud servers can quickly locate affected assets, identify leak paths and restore attack chains when security incidents occur, while providing verifiable evidence for legal/compliance investigations. in addition, through continuous auditing, improper configurations, permission abuse, and abnormal traffic can be discovered and risks can be contained in advance.
it is recommended to proceed according to the following steps: 1) asset inventory and division of responsibilities: clarify all instances, ip segments and services hosted in singapore; 2) log policy definition: specify the log types, formats and retention periods that must be collected; 3) deploy collection and transmission: deploy agents on key hosts and network devices and enable dns and flow logs; 4) centralization and archiving: send logs to siem/elk and make cold backups of important logs; 5) alerts and correlation rules: set alert policies based on behavior detection and ioc; 6) regular audits and drills: conduct audit reviews and evidence collection drills every quarter or after every major change; 7) compliance and least privileges: execute iam policies, key rotation, and access control of audit logs. during the implementation process, ensure that changes are audited and no clear text sensitive data is recorded in the logs.
when logging dns and address queries, the principles of minimization and desensitization should be followed: only save necessary fields (time, source/destination ip, domain name, response code), mask or hash fields containing personally identifiable information, and set strict auditing for log access. follow local pdpa and cross-border transfer requirements, and use data classification and data residency policies when necessary to ensure that sensitive logs are not moved overseas without authorization. for legal hold and evidence collection needs, a preservation process should be developed and the original complete log should be retained for judicial review.
to implement the above strategies, it is recommended to first conduct a round of small-scale poc: select representative systems to start full log collection, verify transmission, indexing and alarm links, and then gradually cover the entire domain and incorporate cost and retention strategies into annual budget assessments.
- Latest articles
- Based On Korean Servers, We Provide Nationwide Security And Compliance Issues And Response Suggestions.
- How Does The Technical Team Reasonably Schedule Vietnam's Native Proxy Ip Nodes In The Crawling Task?
- Analysis Of The Actual Value Of Singapore Host Cn2 Hosting Solution For Website Acceleration Of Foreign Trade Companies
- How To Make Good Use Of The Japanese Amazon Qq Group To Increase Store Traffic And Conversion Rate
- Enterprise Network Upgrade Guide Vietnam Cn2 Line Improves User Access Speed
- Practical Tips On Cost Control And Performance Balance In Vps Deployment In China, South Korea And Japan
- How To Achieve Stable Access To E-commerce And Saas Applications Through Cn2 Us Dedicated Servers
- Key Considerations Regarding Qualifications And Technical Support When Selecting A Service Provider For The CN2 Server Cluster In South Korea
- Recommended Singapore IPLC Dedicated Servers For Security And Compliance – Case Studies On Data Encryption And Dedicated Channel Deployment
- A Practical Guide For Nationwide Deployment Strategies And Network Coverage Optimization Based On Korean Servers
- Popular tags
-
Advantages And Applicable Scenarios Of Lightweight Cloud Servers In Singapore
this article discusses the advantages and applicable scenarios of lightweight cloud servers in singapore, covering server configuration, real cases and data demonstration. -
Can Singapore Vps Connect To Google? Analyze The Secrets Of Network Access
in-depth analysis of the issue of whether singapore vps can access google, and explores the secrets and solutions of network access. -
Usage Scenarios And Cost Performance Analysis Of Lightweight Cloud Server Singapore
an in-depth analysis of the application scenarios and cost performance of lightweight cloud servers in singapore, suitable for users with various needs.